Dashboard
To access the main dashboard in Patchstack App, click on Dashboard from the left-side navigation menu.
Dashboard shows you a general overview of all your WordPress sites:

Vulnerabilities section
Section titled “Vulnerabilities section”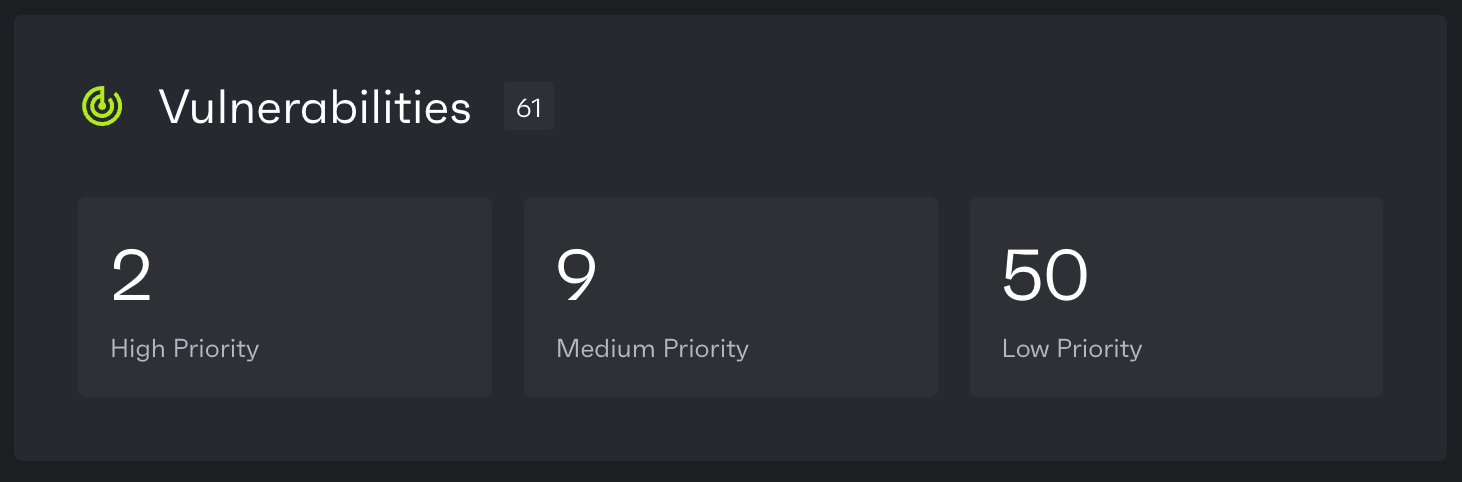
Vulnerabilities section shows you a general overview about all the vulnerabilities currently present on each of your WordPress sites. The vulnerabilities are divided into three different groups, which indicate the patching priority:
-
High patch priority software versions are expected to be mass-exploited or have already known to be exploited vulnerabilities. It’s important to patch those by updating the software to patched versions and/or enabling Patchstack firewall, which applies vPatches automatically.
-
Medium patch priority software versions are not expected to be mass-exploited, but could potentially be exploited in more targeted attacks. It’s important to patch those by updating the software to patched versions and/or enabling Patchstack firewall, which applies vPatches automatically.
-
Low patch priority software versions are not expected to be exploited, therefore low patch priority vulnerabilities won’t receive a vPatch from Patchstack.
Vulnerability information and filtering
Section titled “Vulnerability information and filtering”You can use the search bar on the dashboard page, to find current vulnerabilities across any of your specific sites, or you can search your vulnerabilities by description.
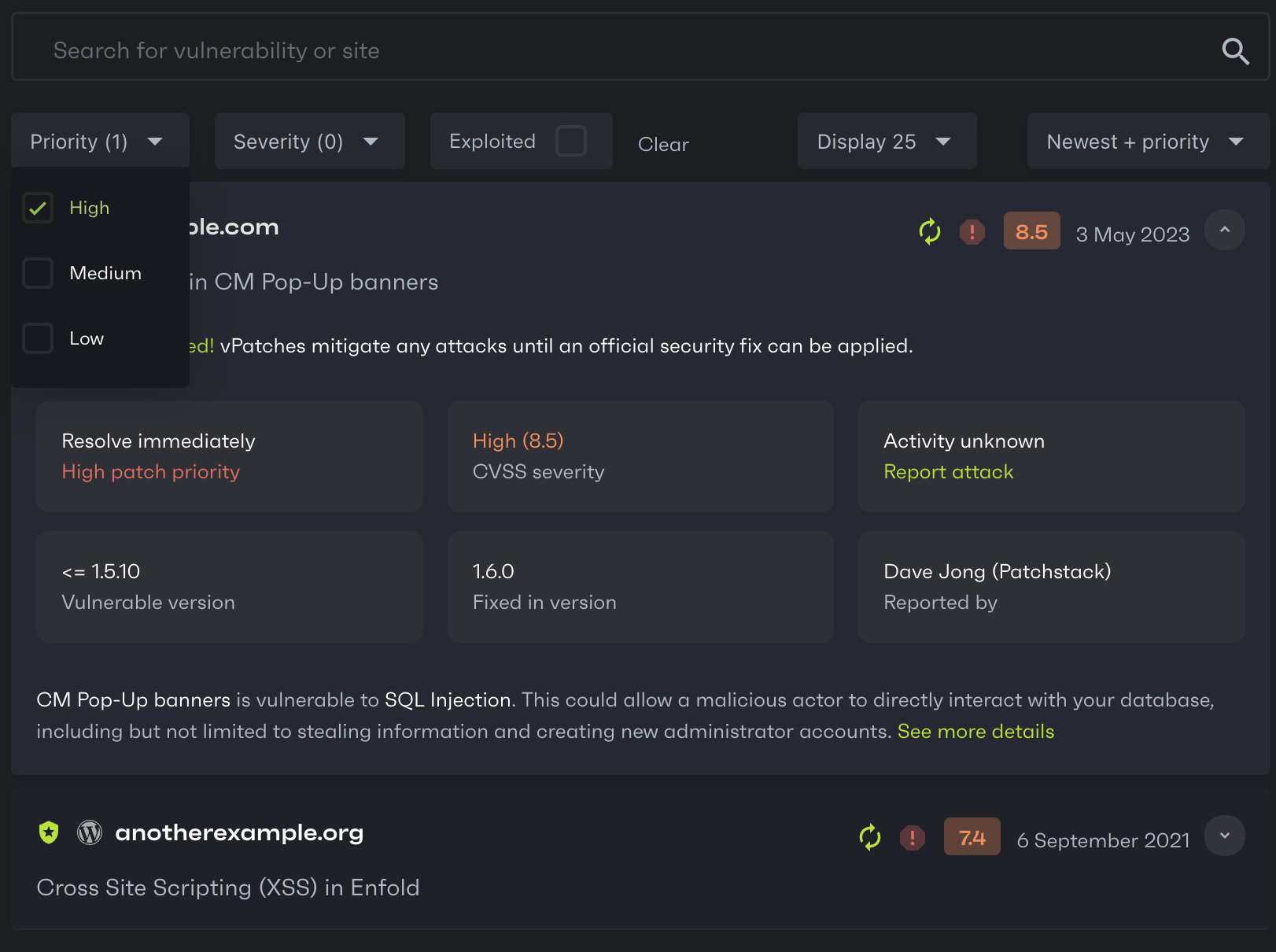
There are three main filters for vulnerability searching on the dashboard:
-
Priority filter - find vulnerabilities by patch priority. You can filter by high, medium and low patch priority vulnerabilities.
-
Severity filter - find vulnerabilities by CVSS severity score. You can filter by critical, high, medium, low severity.
-
Exploited - filter out the vulnerabilities that are know to be exploited.
List of vulnerability icons with descriptions
Section titled “List of vulnerability icons with descriptions”There are several icons shown on each vulnerability row. Below is a list of what each icon means.

No update available
This software is found vulnerable, but it has no updates yet. It is recommended to turn on Patchstack firewall, or to disable and remove this plugin until update is available.

Update available
This plugin has an update available. It is recommended to do this immediately as new software versions usually come with patched code (in case it is found vulnerable).

High patch priority
Red exclamation mark indicates that this software version is expected to be mass-exploited or has already known to be exploited vulnerability. It is recommended to turn on Patchstack firewall as high patch priority vulnerabilities receive a vPatch from Patchstack. Update this software as soon as possible.

Medium patch priority
Yellow exclamation mark indicates that this software version is not expected to become mass-exploited, but could potentially be exploited in more targeted attacks. It is recommended to turn on Patchstack firewall as medium patch priority vulnerabilities receive a vPatch from Patchstack. Update this software as soon as possible.

Low patch priority
Gray exclamation mark indicates that this software version is not expected to become exploited. It is important to update this software when possible, although the security risk is very low. Low patch priority vulnerabilities won’t receive a vPatch from Patchstack.

CVSS score
These numbers represent the CVSS score given to the vulnerability. The higher the CVSS score, the more severe is the vulnerability.
Low (0.0 - 3.9); Medium (4.0 - 6.9); High (7.0 - 8.9); Critical (9.0+)
Threats blocked section
Section titled “Threats blocked section”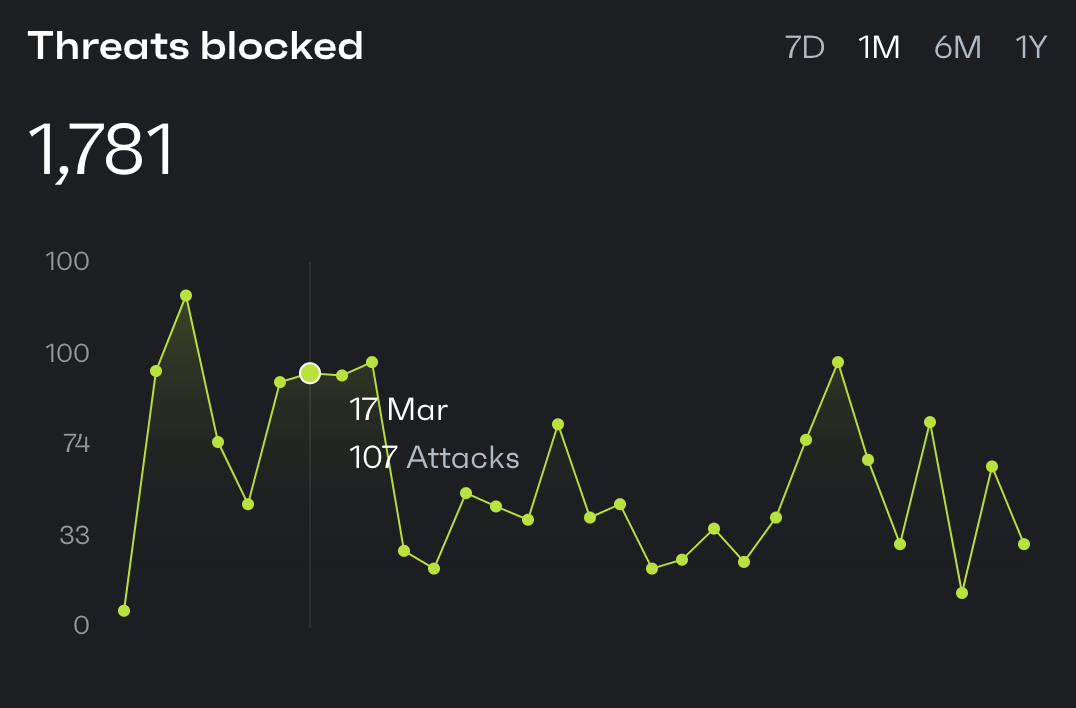
In the Threats Blocked section you can see a graph, which shows you how many attacks have been blocked by Patchstack across all your sites in total.
On the top right corner, you can choose the time period (7 days, 1 month, 6 months or 1 year).
On the left side, you see the number of attacks.
By moving the cursor on the graph, you can see the number of attacks by day.
In the Sites section, you see a quick overview of how many sites you have added to the Patchstack App.
It also shows how many of your sites have any outdated or vulnerable components.
To add new websites to Patchstack App, click the ”+ Add new” button. It will trigger a popup with steps to take to add more websites.
Software
Section titled “Software”In the Software section, you can see how many software components (plugins, themes, WordPress core) your sites have in total.
The next number shows how many of these are vulnerable.
The third number shows how many of these components are disabled.
Reports
Section titled “Reports”In the Reports section, you can see how many reports have been scheduled and how many are available to download.