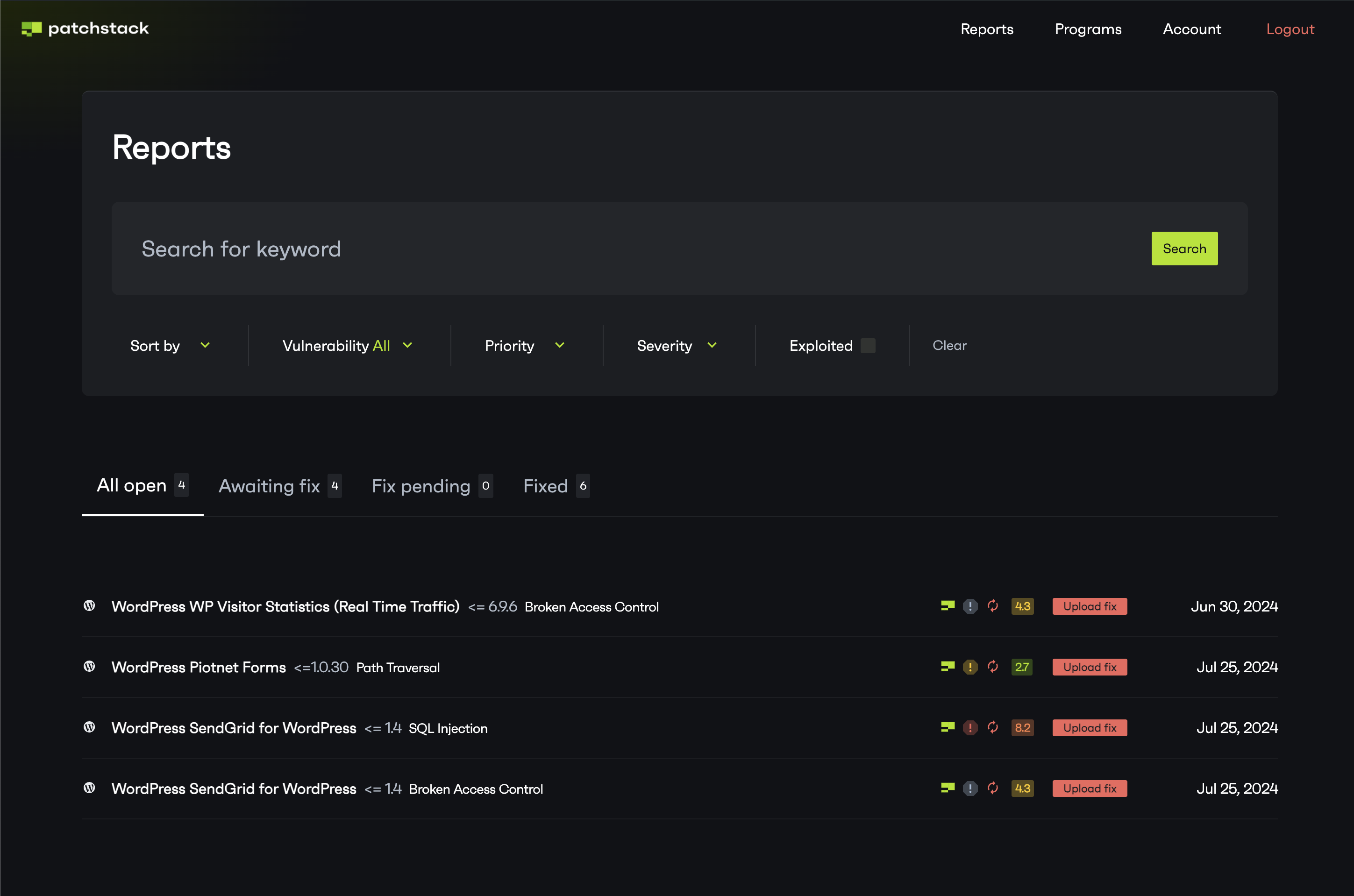
Vulnerability reports dashboard
In your vulnerability reports dashboard, you can see all the data about all the vulnerability reports that have been submitted for your software. In this article, we’ll explain all the details about what the reports dashboard shows you.
Sort and search vulnerabilities
Section titled “Sort and search vulnerabilities”To find specific vulnerabilities, or search for a certain plugin or theme of yours, you can use the filters and searchbar. You can sort your vulnerability reports by following filters
- Sort by - newest / oldest
- Vulnerability type
- Patch priority - low / medium / high
- Vulnerability severity (CVSS) - low / medium / high / critical
- Exploited - choose if the vulnerability is known to be exploited
Vulnerability entries and icons
Section titled “Vulnerability entries and icons”
The entries are listed in the table. Each row shows:
- CMS of that software
- Name of the software
- Versions that are affected
- The icons on the right show the severity score and patch priority level, as well as who published this vulnerability
- On the right side, is a publish date of this vulnerability
By clicking on an entry row, you can see a detailed view of this vulnerability. To understand the icons that are listed in the table, see this article.